Registry Operator's Proposal
¡¡
I. GENERAL INFORMATION
¡¡D1.
Registered name of the company£ºEastern Communications Company Limited.Registered address
£ºNo. 80-84,Wensan Road,Hangzhou,Zhejiang, P.R.China.Tel
£º+86-571-8865383Fax
£º+86-571-8865275¡¡
¡¡
D2.
No other business locationD3.
The registry operator¡¯s type of business entity£ºCompany Limited.The company is organized under the law of People
¡¯s Republic of China.¡¡
¡¡
D4. URL of principal world wide web site:
www.eastcom.com. ¡¡D5. Dun & Bradstreet D-U-N-S Number:
none.D6. Number of employees:
2340.(by the end of June 2000) ¡¡D7. Total revenue (in US dollars) in the last-ended fiscal year:
US$836,603,680.39. ¡¡D8. Names and positions of senior managers:
1)
COO£ºMr.YuchangmingCFO
£ºMr.WangzhongxiongVice President
£ºMr.ZhangzexiVice President
£ºMr.HaoxiaofengVice President
£ºMr.ChenxuhongVice President
£ºMr.YuxudongVice President & Secretary of the Board
£ºMr.ShenyuyinVice President
£ºMr.Guojunfeng2)
All relevant managers:Tao Xiongqiang |
Head of R&D Center |
Li jingjing |
Head of President's Office |
Zhang liangzhong |
Head of Finance Division |
Xu xiaoli |
Assistant of President & Head of Human Resource Divison |
Gu guoying |
Chief of the Business Delegates& Head of Trading Division |
Mao jieming |
Head of Technology Quality Division |
Gu kunming |
Head of Corporate Planning and Management Division |
Shen zhineng |
Head of MCIG (Mobile Cellular Infrastructure Group) |
Lu lixin |
Head of Transmission Equipment Division |
Wang jianzhong |
Head of Electronic Equipment Division |
Chen deming |
Head of Machining Division |
Sun yihao |
Head of Power Equipment Division |
3)
Persons or entities owning five percent or more of registry operator£¨up to 20th Sept,2000£©Zhejiang Eastern Communications Group Co.,Ltd.
£º51.59%Zhejiang Eastcom Holding Co.,Ltd.
£º5.73%D9.
Contact information:1) Name: Chen Jiangping
Tel: +86 571 8865383
Fax: +86 571 8865275
2) Name: Yao Qing
Tel: +86 571 8865020
D10.
No subcontractors¡¡
II. BUSINESS CAPABILITIES AND PLAN
¡¡D11. The second section of the Registry Operator's Proposal (after the "General Information" section) is a description of the registry operator's Business Capabilities and Plan. This section must include a comprehensive, professional-quality business plan that provides detailed, verified business and financial information about the registry operator. The topics listed below are representative of the type of subjects that will be covered in the Business Capabilities and Plan section of the Registry Operator's Proposal.
D13. The Business Capabilities and Plan:
D13.1.1
Company information:Date of formation: 1st Aug,1996
Legal status
£ºLawfully existing£¬under legal management£¬with no momentous lawsuit or disputes.Primary location
£ºNo. 80-84,Wensan Road, Hangzhou, Zhejiang, P. R.ChinaSize of staff
£º2340Formal alliances
£ºMOTOROLA¡¢WINCOR NIXDORF¡¢TEXAS INSTRUMENTS¡¢ARTHURANDERSEN¡¢SIEMENS¡¢QUALTUMM¡¢MICROSOFTOwnership structure(up to 20th Sept,2000)
£ºName of shareholder |
Number of shares |
percentage |
Zhejiang Eastern Communications Group Co.,Ltd. |
324,000,000 |
51.59% |
Zhejiang Eastcom Holding Co.,Ltd. |
36,000,000 |
5.73% |
A Shares |
118,000,000 |
18.79% |
B Shares |
150,000,000 |
23.89% |
Total |
628,000,000 |
100% |
D13.1.2.
Core capabilities
£ºoffer the total solution of mobile networkServices offered
Products offered
£ºCellular Mobile System Equipments, Mobile Telephone, Mobile Network Increment Software, Mobile Network Specialty Service, Light communications Equipments, Laser Typesetter Equipments, Finance Electron Network Products, Information systems Network Products.Duration of provision of services and products
£º1990£¨From its predecessor£©D13.1.3.
Past business operations/entity history.As the predecessor of Zhejiang Eastern Communications Co., Ltd., Zhejiang Posts and Telecommunications Equipment Factory was grew out of Equipment Supply Office of Zhejiang Posts and Telecommunications Bureau in August, 1958. At that time, the factory was principally engaged in the R&D of carrier phone terminal, series equipment for teleconference, dispatcher equipment with super-high frequency and many telecommunications products.
In July 1962, the factory name was changed into Hangzhou Posts and Telecommunications Equipment Factory and it was administrated by the Ministry of Posts and Telecommunications(MPT). In 1970, the General Office of Telecommunications took the place of MPT. Hangzhou Posts and Telecommunications Equipment Factory was governed by the General Office of Telecommunications, it was named by code 522. In June 1981, this code name(522) was changed into Hangzhou Telecommunications Equipment Factory of MPT.
In July 1994, Hangzhou Eastern Communications Chuangye Company was established. As the wholly-owned subsidiary company of Hangzhou Telecommunications Equipment Factory, it
was concentrated with many departments which were in charge of manufacturing and sales of mobile communications equipment. It was registered in Hangzhou high-tech industry developed region.Hangzhou Communications Co., Ltd. was established on 18th April, 1996 and it succeeded to the whole assets and liability of the former Hangzhou Telecommunications Equipment Factory.
On the base of Hangzhou Eastern Communications Chuangye Company, Eastern Communications Co., Ltd.(Eastcom) was established by IPO on 21st May,1996.
B and A shares of Eastcom were listed for transaction at Shanghai Securities Exchange(SSE) on 9th August and 26th November, 1996 respectively.
D13.1.4.
Related experience and activities: EASTCOM is one of ICANN accredited registrar and has full experience in Domain name registration and relevant activities.D13.1.5. Mission. The registry operator's mission and how it relates to expansion into the registry operation field.
We have got ISP license from our government and have accredited by ICANN as a domain name registrar. It is a strategic movement that Eastcom is going to INTERNET fields.D13.1.6. Management.
Mr. Shijixing, chairman of the Board & CEO,aged 58, senior engineer, graduated from Beijing Posts and Telecommunications University in 1967. Mr. Shi is the vice chairman of the Board of Eastern Communications Group Co., Ltd., the deputy President. Mr. Shi was the head of the product research department and the director of the new product institute of HCCL. He was the head of the factory in 1988. Mr. Shi has won many awards, including the 1994 PRC National Excellent Enterpreneur (Golden Ball Award) and the Labour Model of Zhe Jiang Provience. He is recognized as an expert with outstanding contribution to the state and is entitled to a special subsidy from the state.
Ms. Wang Lihua, vice chairwoman of the board,aged 51, senior engineer, graduated from Zhe Jiang University in 1976. She is now the vice chairwoman and the deputy President of Eastern Communications Group Co., Ltd., She was the head of the organization department of HCCL.
Ms. Zeng Yu, director of the board,aged 56, senior accountant, is the President of the finance department of China PTIC Information Industry Corporation. Ms Zeng has held various positions with PTIC including assistant accountants, accountant and a deputy manager in business and finance department.
Mr. Xie Yupu, aged 58, senior engineer, is the vice-chairman of Eastern
communications Co ., Ltd and technical advisor. Mr. Xie graduated from Beijing Posts and Telecommunications University in 1968. Mr. Xie held a number of positions at HCEF, including director of New Products Research Institute, deputy chief engineer and deputy director. Mr. Xie has been awarded the title of Expert with Outstanding Contribution to the State, which award entitles him to receive a special subsidy from the State.Mr. Yu Changming, director of the board & COO,aged 51, senior engineer, graduated from Zhe Jiang University in 1973.Mr. Yu held various positions at HCEF, including head of the production department, assistant to the factory director, head of the director
¡¯s office, deputy director and President of the MCIG division.Mr. Wang Zhongxiong, director of the board & CFO,aged 47, senior economist. he received a university education. Mr. Wang held various positions at HCCL, including secretary to the factory director, head of the finance department and deputy chief accountant.
Mr. Zhang Zexi, aged 45, senior engineer, graduated from college, is the deputy President of Eastern Communications Co., Ltd. He was the head of production department, sales department of HCEF.
Ms. Ni Shouping, director of the board ,aged 36, graduated from college, certified accountant, senior accountant. Ms Ni is the general accountant of Eastern communications Group Co., Ltd. She was the assistant manager of finance department of HCCL and the manager of finance department of Eastern Communications Co., Ltd.
Mr. Pan Yunhe, independent director of the board ,aged 54, graduated from shanghai Tongji University majored in architecture in 1970 and graduated from Zhe Jiang University with Master Degree, majored in computer. Mr. Pan is a computer specialist and academician. He is the president of Zhe Jiang University and graduate school. Since 1990, he has been the director of research institute, dean of computer department and vice president of Zhe Jiang University.
Mr. Gu Jun, independent director of the board ,aged 44, is the chief scientist of China Electrical Information Industry Group Corporation. Mr. Gu graduated from China Science and Technology University majored in electronic engineering in 1982. He got the PhD of computer from Utah University in 1989. He is now the computer professor of Hong Kong Science and Technology University and China Science and Technology University.
Mr. Lu Guanqiu, independent director of the board ,aged 55, senior economist, is the chairman of Zhe Jiang entrepreneur association and Chairman of the Board of Wanxiang Group. The group was established in 1969 and total assets amounted to RMB 5 billion. He was awarded the title of excellent entrepreneur and model worker.
Mr. Shen Yuyin, aged 32, engineer, graduated from Shanghai Tongji University, is the deputy President & secretary to the Board of Directors. He served as an assistant to the director of a branch.
Mr.Hao Xiaofeng, aged 50,master degree,senior engineer,is the deputy President.Mr. Hao held various at HCEF,including head of the information office,head of the technology import office,President of th MCIG division and Trading Division and President of th MCSG Division.
Mr.Chen Xuhong, aged 57, senior engineer, is the deputy President.Mr.Chen has a Bachelor of Science from TsingHua University. He held various positions at HCEF, including head of New Products Research Institute, deputy chief engineer,chief engineer and President of the MCSG Division.Mr. Chen was awarded the title of Expert with Outstanding Contribution to the state,which award entitles him to receive a special subsidy from the State.
Mr.Yu Xudong,aged 46,senior engineer,is the deputy President.He received a university education.Mr. Yu was the deputy director of the Switching Branch of HCEF,President of SPC division,standing vice president of the Great Dragon Telecommunications Equipment Co.,Ltd., president of the Marketing Group of Eastern Communications Group Co.,Ltd.
Mr. Guo Junfeng, aged 31, engineer, graduated from Shanghai Science and technology University with bachelor degree in 1990 and graduated from Zhe Jiang University with MBA in 1998. He is the deputy President & the President of Terminal Communications Products Sales and Marketing Group. He served as assistant manager of R&D Center and the deputy President of Subscriber Division.
D13.1.7. Staff/employees.
The number of current staff in the company is 2340
£¬73% of whom have bachelor¡¯s degree or above, and more than 140 have master¡¯s or doctor¡¯s degree. Among these staff, 33% are scientific research personnel£¬32% are marketing & service personnel, 25% work as manufacture personnel£¬and the other(10%) are manage personnel.D13.1.8. Commercial general liability insurance. Address/include amount of insurance policy, provider of policy, plans for obtaining additional insurance.
Total value of the insurance is RMB 1.2 Billion (about US$144.6 Million).
Details see Annex D_6.
D13.2. Business plan for the proposed registry operations. This section should present a comprehensive business plan for the proposed registry operations. In addition to providing basic information concerning the viability of the proposed operations, this section offers the registry operator an opportunity to demonstrate that it has carefully analyzed the financial and operational aspects of the proposal. At a minimum, factors that should be addressed are:
D13.2.1. Services to be provided. A full description of the registry services to be provided.
Domain registration, renewal , transfer, modification, etc., the same as NSI.
Whois service, the same as NSI.
Other services detailed in ICANN-NSI agreement.
¡¡
D13.2.2. Revenue model. A full description of the revenue model, including rates to be charged for various services.
We suppose EASTCOM will adopt the same revenue model as NSI at the beginning of its operation.
Only register service is considered chargeable, and the yearly fee for per new or extend domain name registration is US$6.00.
¡¡
D13.2.3. Market. Market definition, size, demand, accessibility.
All internet users are our potential customers. The market size is 170 million or so in 1999 and the market is booming and the figure of customers will be expected to 600 million by the end of 2001, which shows a great market in the area of internet.
Among this market size more than 5% is willing to obtain its own domain name in the new TLD, which will consist of the market demand of domain name.
Among the market demand more than 10% is willing to register its own domain name in the new TLD.
¡¡
D13.2.4. Marketing plan. Advertising, publicity, promotion strategy, advertisement development strategy, relationship with advertising firm. Use of registrars and other marketing channels.
Eastcom has good relationship with some famous advertising firm, consulting firm, website, and other media unit, which will become Eastcom
¡¯s publicity channels. Eastcom also has the throughout sales network to promote, distribute, sale its products and provides the relevant services. All the above-mentioned publicity channels and network will consist of the main marketing channels of new TLD. Besides, Eastcom will designate registrars as the other main marketing channels.D13.2.5. Estimated demand for registry services in the new TLD. Projected total demand for registry services in the TLD, effect of projected registration fees, competition. Please provide estimates for at least 10%, 50%, and 90% confidence levels.
The total demand for registry services in .shop TLD will reach about 10 million, if the registration fees keep the same level as in .com, and it will cause limited competition in the field of registration. We have full confidence of this.
As to the other TLD strings we suppose in this application, the total registration volume may be less, but if some competitive price policy be adopted , they certainly have their own value. One thing is doubtless , they all will lead to the same result: bring some proper competition in the field, and this will help the DNS grow in a more reasonable way.
D13.2.6. Resources required to meet demand. Provide a detailed estimate of all resources (financial, technical, staff, physical plant, customer service, etc.) required to meet the estimated demands, using at least the 10%, 50%, and 90% confidence levels.
Details see Annex D_1.D13.2.7. Plans for acquiring necessary systems and facilities. Describe plans for acquiring all necessary systems and facilities for providing the proposed services at each estimated demand level. Provide details as to the scope, cost, and vendor for any significant planned outsourcing.
It is most likely that the demand peak of registration will occur at the beginning, so we should take this situation into consideration when we choose network equipment and database software. Using application software with multi-layer structure to provide service take the advantage of better scaleable, and this can be achieved easily whenever it
¡¯s necessary.| Product | Vender |
Price |
Quantity |
Sum |
Remark |
| UDB Enterprise Extended Edition for AIX | IBM |
US$250,000 |
4 |
US$1,000,000 |
One set per site |
| RS/6000 Cluster | IBM |
US$500,000 |
4 |
US$2,000,000 |
Database Server |
| PC Server | IBM |
US$50,000 |
50 |
US$2,500,000 |
Including Application Server and Backup Server |
| Backup Software and Hardware | IBM & CA |
US$100,000 |
4 |
US$400,000 |
Database Backup |
| Registry Software | EASTCOM |
US$500,000 |
1 |
US$500,000 |
¡¡ |
| Network management & relevant software | Cisco & CheckPoint |
US$200,000 |
4 |
US$800,000 |
¡¡ |
| Network Equipment | Cisco |
US$250,000 |
4 |
US$100,000 |
¡¡ |
| Sub total | ¡¡ | ¡¡ | ¡¡ | US$8,200,000 |
¡¡ |
| Standby | ¡¡ | ¡¡ | ¡¡ | US$300,000 |
For other equipment |
| Total | ¡¡ | ¡¡ | ¡¡ | US$8,500,000 |
¡¡ |
Every 10,000,000 additional registrations needs following investment
£º| Product | Vender |
Price |
Quantity |
Sum |
Remark |
| RS/6000 | IBM |
US$200,000 |
4 |
US$800,000 |
¡¡ |
| PC Server | IBM |
US$50,000 |
10 |
US$500,000 |
Provide Whois service |
| Total | ¡¡ | ¡¡ | ¡¡ | US$1,300,000 |
¡¡ |
Every 10 additional registrars needs following investment
£º| Product | Vender |
Price |
Quantity |
Sum |
Remark |
| PC Server | IBM |
US$50,000 |
6 |
US$300,000 |
Application Server |
| UDB License | IBM |
US$20,000 |
10 |
US$200,000 |
Client access license |
| Total | ¡¡ | ¡¡ | ¡¡ | US$50,000 |
¡¡ |
¡¡
D13.2.8. Staff size/expansion capability. Plans for obtaining the necessary staff resources, capacity for expansion, hiring policy, employee training, space for additional staff, staffing levels needed for provision of expanded technical, support, escrow, and registry services.
More than 300 professional people will be employed to execute this project. The total staff will reach 500 in the next two or three years. In China more and more people pay more attention to the IT industry which provides enough human resources. Eastcom will provide competitive salary, option stock and long-term training to employ enough technical staffs. Eastcom is now constructing Eastcom City with the area of more than 300,000 square meters of which will be designated to the special space for additional staff.
D13.2.9. Availability of additional management personnel. How will management needs be filled?
Eastcom will designate one VP who directly report to CEO, in charge of this project and such project has the priority to obtain all resources such as financial, staff, technical, physical demands, etc.. During the next several years, such project will be developed as the main business of Eastcom.
D13.2.10. Term of registry agreement. State assumptions regarding the term of any registry agreement with ICANN or the sponsoring organization. Note that the .com/.net/.org registry agreement has a basic term of four years.
5 year.
D13.2.11. Expected costs associated with the operation of the proposed registry. Please break down the total estimated operational costs by the sources of the costs for each estimated demand level. Be sure to consider the TLD's share of ICANN's cost recovery needs. (See <>.)
Details see Annex D_1.
D13.2.12. Expected revenue associated with the operation of the proposed registry. Please show how expected revenue is computed at each estimated demand level.
Details see Annex D_1 .
D13.2.13. Capital requirements. Quantify capital requirements in amount and timing and describe how the capital will be obtained. Specify in detail all sources of capital and the cost of that capital (interest, etc.). Evidence of firm commitment of projected capital needs will substantially increase the credibility of the registry operator's proposal.
D13.2.14. Business risks and opportunities. Describe upside and downside contingencies you have considered and discuss your plans for addressing them.
The registration quantity is main business risk and opportunity. If the registration quantity can
¡¯t reach the expected volume, Eastcom will keep on promoting the project.D13.2.15. Registry failure provisions. Please describe in detail your plans for dealing with the possibility of registry failure.
Although EASTCOM will use all the possible technical method to avoid such failure, we know for sure the commercial preparation for such occasional failure is necessary. We will minimize the loss from such a failure by commercial insurance and third-party guarantee.
Details see D15.2.12.
D13.3. Pro-forma financial projections. Please provide detailed pro-forma financial projections, consistent with your business plan, for the demand scenarios that you estimate under item D13.2.5. The pro-formas should show revenue and expense estimates broken down by detailed categories and should be broken down into periods no longer than quarterly.
We have made a 5-year financial project of this registry operation. And you can get all the detailed information from Annex D_1.
D13.4. Supporting documentation. The following documentation should be provided in support of the Business Capabilities and Plan section:
D13.4.1. Registry operator's organizational documents. Documents of incorporation (or similar documents).
Details see Annex D_2
D13.4.2. References. A list of significant trade and credit references.
Details see Annex D_3
D13.4.3. Annual report. The registry operator's most recent annual financial report (or similar document). Audited financials are preferred.
Details see Annex D_4
D13.4.4. Proof of capital. Provide evidence of existing capital or firm commitments of capital. Demonstrated access to necessary capital will be carefully scrutinized.
Details see Annex D_5
D13.4.5. Proof of insurance. Please provide proof of the insurance described in item D13.1.8.
Details see Annex D_6
III. TECHNICAL CAPABILITIES AND PLAN
D14. The third section of the Registry Operator's Proposal is a description of the registry operator's Technical Capabilities and Plan. This section must include a comprehensive, professional-quality technical plan that provides a detailed description of the registry operator's current technical capabilities as well as a full description of the operator's proposed technical solution for establishing and operating all aspects of the registry. The technical plan will require detailed, specific information regarding the technical capabilities of the proposed registry. The topics listed below are representative of the type of subjects that will be covered in the Technical Capabilities and Plan section of the Registry Operator's Proposal.
[ICANN will extensively review and analyze this section of the Registry Operator's Proposal. The content, clarity, and professionalism of this section will be important factors in ICANN's evaluation of applications. We strongly recommend that those who are planning to apply secure professional assistance from engineers and/or other technical consultants to aid in the formulation of the technical plan and the preparation of the Technical Capabilities and Plan section of the Registry Operator's Proposal.]
¡¡
D15. The Technical Capabilities and Plan section should consist of at least the following:
D15.1. Detailed description of the registry operator's technical capabilities. This should provide a detailed description of the registry operator's technical capabilities, including information about key technical personnel (qualifications and experience), size of technical workforce, and access to systems development tools. It should also describe the registry operator's significant past achievements. This description offers the registry operator an opportunity to demonstrate the extent of its technical expertise in activities relevant to the operation of the proposed registry.
technical capabilities of Eastcom, including
£ºname |
Degree |
Graduate academy |
Major |
Project engaged Now |
||||
Tao Xiongqiang |
Doctor |
Zhejiang university |
Information and Electricity |
Director of R&D Center |
||||
Wu Yue |
Doctor |
Zhejiang university |
Biomedical Engineering and Instruments |
ATM B-band Switch Platform |
||||
Yang Haibo |
Doctor |
Zhejiang university |
Communication and Information System |
ATM B-band Switch Platform |
||||
Ye Jun |
Doctor |
Zhejiang university |
Measurement and test Techniques and Instruments |
Collectivity design of SDH transmission equipment |
||||
Wang Chao |
Doctor |
Shanghai Tongji University |
Image dispose and Pattern Recognition |
CDMA switch |
||||
Cheng Xiaoxiong |
Doctor |
Shanghai Jiaotong university |
Image Communication |
CDMA switch |
||||
Zhang Zheliang |
Doctor |
Zhejiang university |
Biomedical Engineering and Instruments |
Design main control software of CDMA switch |
||||
Qian Guoliang |
Doctor |
Harbin institute of technology |
Computer application |
In charge of SDH transmission equipment and access network equipment |
||||
Luo jianjun |
Doctor |
Zhejiang university |
semiconductor |
ASIC design |
||||
Li Wenhua |
Doctor |
East-south university |
Communication and Signal Processing |
ATM B-band Switch Platform |
||||
Yang yongkang |
Master |
Shanghai Jiaotong university |
Communication and Electric System |
Senior engineer |
||||
Kang jian |
Master |
China spin university |
Automation |
In charge of ATM B-band Switch Platform |
||||
Ding ta |
Master |
Zhejiang university |
Communication and Electric System |
SDH transmission equipment |
||||
Yao junwu |
Master |
Xian Jiaotong university |
Applied Mathematics |
Design main control software (Signaling and protocol) of CDMA switch |
||||
Cheng yuxin |
Master |
Zhejiang university |
Microwave technology |
Design Network Management of SDH transmission equipment |
||||
Huang chaoyang |
Master |
Zhejiang university |
Machine |
Product Design |
||||
Chen chi |
Master |
Zhejiang university |
Test Techniques |
Design main control software of SDH transmission equipment and access network equipment |
||||
Cao yu |
Master |
Zhejiang university |
Optical instrument |
SDH transmission equipment |
||||
Za hongmei |
Master |
Zhejiang university |
Detect |
Design MSC main control software CDMA switch |
||||
Guo jianping |
Master |
Zhejiang university |
Precision instrument |
SDH transmission equipment and access network equipment |
||||
Cao yu |
Bachelor |
Shanghai teachers unversity |
Computer application |
Software designer |
||||
Yao qing |
Bachelor |
Fudan university |
Autocontrol |
Senior systems engineer |
||||
Jin hua |
Bachelor |
University of electronic science and technology of china |
Compunication |
Senior network engineer |
||||
Zheng jian zhong |
Bachelor |
Lanzhou university |
Computer |
Senior Software engineer |
||||
Miao yajun |
¡¡ | Fudan university |
Administrative Management |
Web designer |
||||
Cai jun feng |
¡¡ | Zhejiang institute of electronic technology |
Computer application |
network engineer |
||||
¡¡
¡¡
¡¡ Name |
Degree |
Graduated academy |
speciality |
post |
Zhang bing |
Bachelor |
Zhejiang university |
Communication and electronic |
systems engineer |
Wu fei |
Bachelor |
Xi an highway university |
Computer application |
Senior Software engineer |
Chen jiangping |
Master |
Zhejiang university |
MBA/computer |
Department director |
Cen kai |
Bachelor |
East China University of Science and Technology |
Polymer science & Engineering |
Senior engineer |
Weng ting |
Bachelor |
¡¡ | Wireless communication |
Senior Software engineer |
Jiang yongjun |
Bachelor |
Hangzhou institute of electronic technology |
Electronic application |
Senior Software engineer |
Kong tianmiao |
Master |
Zheng Jiang University of Technology |
Mechanization Engineering |
Senior Software engineer |
Lin xiaoyue |
¡¡ | Zhejiang radio and television university |
Engineering Electrical |
Software engineer and system engineer |
Wan zhaobing |
Bachelor |
Hangzhou university of commerce |
Economy and communication |
Network engineer |
Chen huapeng |
Master |
Zhejiang University |
Computer science |
Senior Software engineer |
Gao liqiang |
Bachelor |
Hangzhou institute of electronic technology |
Computer |
system engineer |
¡¡
D15.2. Technical plan for the proposed registry operations.
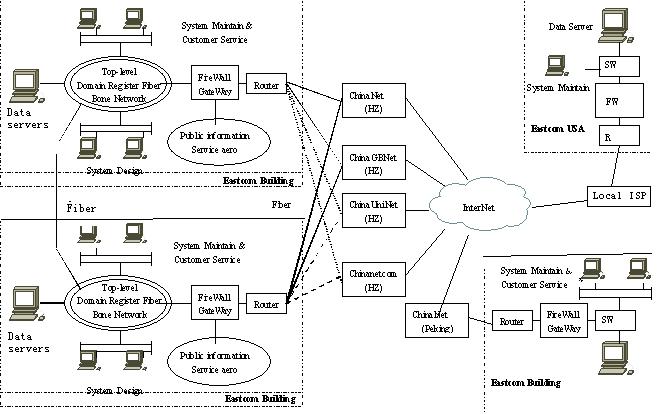
Network Topolopy
¡¡
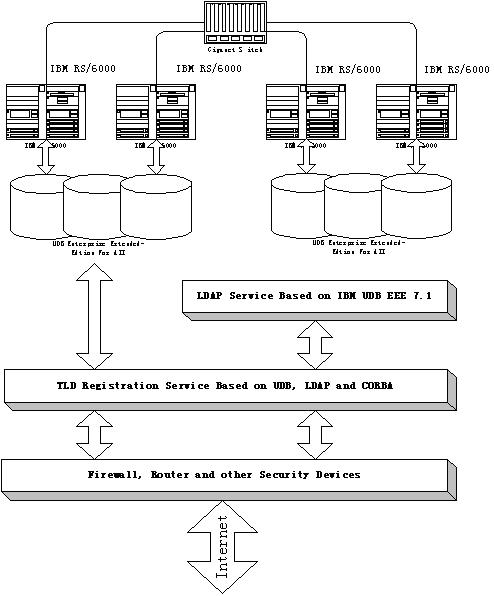
Data Servers
¡¡
D15.2.1. General description of proposed facilities and systems
Eastcom new TLD registry system is regionally divided into 4 parts: Eastcom Building, Eastcom City, Eastcom Peking, Eastcom USA. Please refer to the network topological graph. Most network facilities are provided by Cisco.
Eastcom Building (Building Introduction): As a standard computer room, it is 2000 square meters by area, equipped with high-power constant temperature and constant humidity air-condition, UPS and lightning proof system, etc. Up till now, it has been connected to the ChinaNet, ChinaGBNet via fiber and plans to be connected to ChinaUniNet and ChinaNetCom as well. Its intra backbone network adopts fiber Gigabit Ethernet technology, and principal database servers are directly connected to backbone switch through fiber interface. In order to ensure the system security, Checkpoint FireWall I and hardware firewall are installed on the Gateway Server. At the same time, ISS network monitor software is applied to monitor and control the flux on the net.
Eastcom City: It has the similar equipment to the system of Eastcom Building. The switches in the above two sites are connected by fiber, 35 kilometers by long. As another part of the TLD Registry System, it takes charge of user authentication, the registry, system development, data backup, etc. By configuration of IP address of registrar and client application, the registry balance between Eastcom Building and Eastcom City could be fulfilled.
Eastcom Peking: Gigabit Ethernet technology adopted on intranet backbone, principal database server connected with backbone switch through fiber NIC, FireWall I installed between intranet and internet, this site takes charge of WHOIS query, client service, database backup, etc.
Eastcom USA: Fiber Fast Ethernet technology adopted on Inner backbone, principal database server configured with 100M NIC, FireWall I installed between inner net and Internet, this site takes charge of data backup.
Function and interactive: All the servers from the above sites are equipped with the complete business procedures, however, they could open different process according to separate functions. Under normal conditions, the registry workload is kept balance by Eastcom Building and Eastcom City. Whichever site falls into problem, the other site will automatically take over all the registry business. If trouble falls on both, Eastcom Peking will take over the registry within 24 hours. Only when the above three networks fail, Eastcom USA turns on the whole business. The WHOIS query is mainly in charged by Eastcom Peking. Eastcom Building and Eastcom City share the business in a balanced way. If the disaster occur, only when the above three networks fail, Eastcom USA gets down to start all registry business.
Details see Annex D_7.
D15.2.2. Registry-registrar model and protocol
As an ICANN-accredited registry organization, we do not accredit new registry-registrar independently. All ICANN-accredited registrars will be registry-registrar of the new TLDs automatically. We will provide the new TLDs¡¯ registry-registrar with registry interface software and essential technical support. Along with the registrars, we are responsible for the maintenance and popularization of the TLDs.
We plan to develop a new Registry-Registrar protocol and design the relevant software. Our technical capability (see D15.1) is enough for developing a complex and powerful Registry-Registrar protocol.
D15.2.3. Database capabilities
We think that database subsystem is a critical part of the TLD Registry System. Especially after the deployment of DNSSEC, the amount of disk space and RAM consumed by signature and privacy-key information will be more than 10 times of the amount the registry information itself. To satisfy the requirement of capacity, high throughput and scalability, we will adopt the DBMS with highest performance: IBM UDB Enterprise Extended Edition 7.1. DB2 Universal Database supports the following key capabilities and benefits:
Superior scalability - DB2 Universal database can run on everything from laptops supporting mobile users to massively parallel systems with terabytes of data and/or thousands of users. It is the only database in the industry capable of scaling this breadth of systems with the same function. This allows you to minimize costs and maximize personnel skills by using a single database for all your application needs no matter what the scale. You can also rest assured that your applications will not fail because your database ran out of gas.
Multimedia extensibility - DB2 Universal Database allows you to extend the capabilities of the database to meet your specific organizational requirements. This includes the ability to support more advanced applications involving multimedia data such as documents, images, audio and video. You can now develop applications that use technology to gain competitive advantage in ways not previously possible or practical - and you can save costs by just extending DB2 to support these new applications.
Complete web-enablement - One of the key new application areas is e-business. DB2 Universal Database is fully integrated with web technology so that data can be easily accessed from the Internet or from your intranet with complete security. This allows you to quickly build e-business or Internet applications that will provide competitive advantage, greater customer service or reduced costs.
Universe of partner solutions - DB2 Universal Database is capable of supporting a broad range of data management applications with excellent performance and reliability. As a result, a large number of industry solution providers, including SAP, Baan, Peoplesoft, Seibel and thousands more, have adopted DB2 to support their applications; or adapted their tools to support DB2. This allows you to more quickly satisfy your requirements by buying rather than developing solutions.
Business intelligence powerhouse - DB2 Universal Database has particular strengths in supporting business intelligence applications such as data warehousing and on-line analytical processing (OLAP). DB2 leads the industry in parallel database technology and query optimization resulting in the proven ability to help customers find competitive advantage, better customer service or reduced costs by mining their data for the knowledge required to make better decisions. Further, this does not require the additional expense of a specialized database. DB2 UDB provides a single database that can be used across an enterprise for all data management requirements from OLAP to OLTP.
Ease of use and management - DB2 Universal Database is one of the easiest databases in the industry to set up, use and manage. It includes a complete suite of GUI administration tools that allow for easy installation, administration and remote operations. It includes programmer-friendly tools to get an application up-and-running quickly, and user-friendly tools to make end-users immediately productive. Everything you need comes in the box, ready to go.
Universal access - DB2 Universal Database can be accessed from almost any client workstation over almost any network. Through built-in data replication and distributed transactions, it provides you with the flexibility of placing data anywhere in your network required for optimum service and productivity. Further, DB2 provides the most efficient and seamless integration of data on mainframe and midrange data servers in the industry allowing you to reduce costs and improve cycle-times by leveraging your current investments in data, hardware, software, and skills.
Multi-platform support - DB2 Universal Database is one of the most open database platforms available. It runs on the most popular UNIX and Intel server platforms including AIX, HP-UX, Solaris, Linux, NUMA-Q, OS/2 and Windows NT/2000. It supports all major industry standards relevant to distributed data so that it can be accessed using thousands of existing tools and applications, and can be easily managed within an open, network computing environment. These capabilities allow you to reduce costs and improve cycle-times by leveraging your current investments in data, hardware, software, and skills.
Bullet-proof reliability - DB2 Universal Database is setting the standard for quality and reliability in the client/server database industry. As more mission-critical applications are implemented on UNIX and Intel platforms, IBM's ability to bring mainframe-level reliability to this environment has become a major factor in choosing DB2. Better reliability and availability can reduce your costs, while scalability both within and across platforms can reduce the risk of dead-end projects.
Market leadership - IBM entered the client/server database market late. However, with it's core competency in database technology and it's renewed emphasis on software marketing, IBM has delivered more high-quality database technology to market faster than anyone else in the industry. DB2 Universal Database is the culmination of this effort. With DB2 Universal Database, you can rest assured that you are getting the best database technology available today from a vendor with a bright future and the best record of service and support in the industry.
IBM's DB2 Enterprise-Extended Edition 7.1 database leapt to the top of the Transaction Processing Performance Council's TPC-C database benchmark record list this week, providing compelling evidence for the stability and scalability of DB2 7.1 shared-nothing clusters deployed on large numbers of commodity servers. Its performance is 68% higher than the second.
£¨440879tpmC vs. 262243tpmC¡¡262243tpm£©Since registry data organization is hierarchical and the update frequency is much more frequent than the query one, the DNS will be better implemented by using the LDAP technology. So the DNS service will be constructed on the base of LDAP service. And the security of the DNS data can be ensured by the LDAP Server. The DNS acts as the client of LDAP. At the same time, the DNS acts as a CORBA object. Then the DNS data can be asynchronously updated with the help of the Notify Service defined in CORBA. The asynchronous data updating is better than the synchronous one, which will make the Root Server update its data at any free time during processing the normal service and avoid the occurrence of the congestion. The amount can be set when data are updated each time. Many a small updates can be combined to form an asynchronous update so that the network traffic cost of updates will be minimized. If the continuous peek time caused by normal service surpass the interval could be tolerated between two data updates, it shows that the computing capacity of the DNS Server need to be upgraded. The use of Cluster computing makes the upgrade easer and cheap. The reporting capacity could be provided by the OLAP module of the UDB EEE.
D15.2.4. Zone file generation
Zone files are created dynamically. Using the asynchronously updating mode, the amount of data during each update is small. Zone files are created in an accumulative way while the procedure for changes is executing. We define the update frequency as two levels: high frequency (the interval can be configured, such as 6 hours) and low frequency (the interval can be configured, such as 6 days). High frequency zone file is created while updating. After 6-days¡¯ accumulation high frequency zone files will be combined to form a low-frequency zone file. The two kinds of zone files are both the objects of backup. High-frequency zone files can be deleted after they are combined into low-frequency zone files.
When receiving the zone file update request from registrars, the system will do the user authentication to make sure the request is submitted by the registrar of this domain. If it is accepted, the system will generate the zone file of this domain. Otherwise it will deny the request. When the registrar submits the update request, the system will connect it by registry protocol. During the connection, the registrar provides its IP address and its security certificate, using its password and account to login. Because the request submitted by the registrar is completed by program, the program user interface is not graphical. What the graphical interface user will see is provided by the registrar.
D15.2.5. Zone file distribution and publication.
Zone file distribution and publication proceed whenever a high-frequency zone file comes into being. It should be pointed out that directly transmitting of high-frequency zone file is in a mechanism of Incremental transfer (IXFR). Support should be offered if currently used root server only supports full zone transfer mechanism (AXFR). The zone file distribute and publication in the mode of AXFR could be created by combination of high-frequency zone file and relevant low-frequency zone file. Root server validates the identity of each zone file provider via password, accounts, security certificate and security protocol. Since the submitted data are significantly important to the stable of the whole Internet, root server should not accept them until it has sufficiently authenticated the identity of zone file provider. Transmitted data should be encrypted and it should be guaranteed that the identity of zone file provider has no way to be faked.
D15.2.6. Billing and collection systems.
An ERP system will be adopted as billing and collection systems, Products of SAP, Oracle, IFS are under consideration.
D15.2.7. Data escrow and backup.
Backup procedure: In the database system, there stores two copies of registry data, which locates in different databases. Before the backup, it is required to stop the synchronization between the backup data file and online database first, then to proceed the database backup applying the control in ARC Server IT. Then, after completing the backup, to synchronize the backup data file and online database until the next backup. Each set of backup data will have two copies, one in the computer room and the other sent to the third party for saving. At the beginning of each week, we designate a certain responsible person to deliver last week¡¯s incremental backup and this week¡¯s full backup to the third party.
Backup strategy: Since the TTL in the database of currently used name server is 6 days, we could constitute backup strategy once a week. Each week, to full backup the data in database, then to incrementally backup the data every 12 hours. As a complementarity, we copy the full backup on CD-ROM and also send it to the organization of data security for saving.
Hardware and system: We apply tapes for daily backup, using ARC Server IT backup software of CA company for data backup. Since the amount of data is particularly large and special server and backup facility are adopted to proceed data backup and recovery, we make use of compressed-tape data format for backup. Thus we could reduce the frequency of tape-replacing without influencing the speed of data backup and recovery. In case of information leakage due to losing medium, we encrypt the data in the tape.
Escrow Agent
£ºEastcom will deposit into escrow all Registry Data on a schedule (not more frequently than weekly for a complete set of Registry Data, and daily for incremental updates) and in an electronic format mutually approved from time to time by Eastcom and ICANN, such approval not to be unreasonably withheld by either party. The escrow will be maintained by a reputable escrow agent mutually approved by Eastcom and ICANN, such approval also not to be unreasonably withheld by either party.Others: Distributed database applied, we divide the database into data files according to distinct domain name¡¯s heading letter, and as to the leading letter with relatively large number of domain names, division is also employed in term of certain rule. As a result, the speed of recovery is increased and the system¡¯s reliability is enhanced.
D15.2.8. Publicly accessible look up/Whois service.
We are going to develop a set WHOIS Services with a multi-tier structure. Several database servers make up of the data layer, which can improve the query speed and be of a sound scalability. The transaction processing layer also owned several servers for the sake of workload balance, and necessary scalability. The above two layers are connected by Gigabyte Ethernet, while the transaction processing server directly connected to Internet backbone (with firewall in the middle). We provide other WHOIS servers with standard WHOIS query interface and provide WHOIS servers which are under the management of ICANN and registrar with a dedicated line.
D15.2.9. System security.
The Eastcom¡®s new TLD registry system security is fulfilled by hardware firewall, software firewall product (Checkpoint FireWall I) and network security monitor software (ISS).
Registrar authentication: certificate (issued by the third party) authentication bases on client IP address; system administrator decides what resources and programs the user is allowed to access, when he can access and how many sessions can be set up, and etc.
Data Transfer Encryption: The four sites of our system are connected to Internet, so the data transferred should be encrypted. We use the FWZ encryption method (encryption and privacy key management method provided by FireWall I) and DES encryption algorithm. These methods encrypt different packets with distinct keys and make the packets¡¯ size unchanged at the same time.
Content Security: FireWall I provides content security monitor API for the HTTP, SMTP and other protocols by its secure sever. Integrated with OPSEC Alliance API, the system can protect the content security from virus, malice JAVA and ActiveX. At the same time, it will provide the optimized Internet service.
The key equipments used in our system, such as routers, switches, are protected by the access control list based on port, ensuring that only the workstations of some network addresses can access them so that attacking these equipments is prevented.
Most of the network equipments we use are produced by Cisco. We can deploy Intelligent secure network with the Cisco product. Cisco is a point-to-point secure solution provider. The secure products of Cisco include :
To face the possible DNA (Distributed Network Attacks) in the future, we will develop our own resistance method to prevent DNA and cripple the attack. The following measures will be taken:
To run the system smoothly, the following measures will be taken:
D15.2.10. Peak capacities.
The System is designed to have 3-tiers, which makes the developers concentrate on the logical analysis, design and development of the core business in the application system. It also simplifies the system¡¯s development, updating, and upgrading, improves the emergency-dealing ability, problem-solving ability when facing unpredictable suddenness (for instance, peak value phenomenon), and increases the processing speed. Distributed architecture brings us the solution with high fault tolerance, satisfied scalability, high performance. Without doubt, multi-tier architecture is the best choice to implement Internet Service. In a distributed application system with fault tolerance ability and workload balance ability, several application servers, which appear to be one on the client side, offering the same service, is able to dynamically balance the workload submitted by client-side applications and web servers, which means the system can provide services from any server according to the current workload.
We momentarily monitor the system¡¯s execution efficiency, resource usage and other important information when the application is online, which let the developers be able to find out the bottleneck of the application system and adjust it in time. Since the distributed system demands working on a 7-day/24-hour basis, with high-efficiency and stability, we will employ the remote automatic monitor system and momentarily obtain the running states of the large number of objects and transactions distributed on the net, which turns out that when simple problem happens, the monitor system is capable of automatically dealing with them without the interference of administrators, which guarantees the distributed system maintaining stable and secure running state. In addition, in the procedure of monitoring, the system periodically save the configuration information, capacity information, log, etc in order to ceaselessly consummate the system.
In one word, we promise to provide a registry system with high-reliability, high-efficiency, powerful computing capacity of heavy load. The system could definitely give out the fastest solution to problems.
D15.2.11. System reliability.
Definition: To evaluate the system¡¯s reliability in the light of crash hours per year, customers¡¯ complained response time and other parameters.
Analysis: For the unreliable factor, to dig out the concrete reason layer by layer, work out optimized solution and to enhance it in time.
Quantification:
Level A: crash time<5 hours per year service response time< 1 hour
Level B: crash time<12 hours per year service response time< 5 hour
Level C: crash time<24 hours per year service response time< 10 hour
D15.2.12. System outage prevention.
The key facilities on each node of Eastcom new TLD registry system, for instance, advanced router, advanced switch, utilize redundancy configuration, including Supervisors, Uplinks, Clocks, Fabrics, power supplies, load-sharing fans, etc. Principal server employs Cluster computing to realize workload balance and data security. In order to reduce the network congestion as much as possible and ensure the connection to Internet, we select a number of ISP to connect to with fiber (backup fiber included). Currently, connected ISPs involve ChinaNet and ChinaGBNet, and we plan to connect to ChinaUniNet and ChinaNetCom as well. Principal database servers are configured with automatic tape backup facility, living up to daily backup. To take the irresistible factors into consideration, database and data files in the four sites mutually backup, with Eastcom Building as network principal site, Eastcom City as network local backup, in the hope that under normal conditions, the system is able to balance the registry applications and when encountering suddenness, Eastcom City can take over all the business. At the same time, in order to further enhance the data security, we set up data backup in Eastcom Peking and Eastcom USA, ensuring the integrity and security. The system adopts Cisco Works 2000, which can locate bottleneck, mark the equipment causing the largest delay, monitor workload balance capacity of servers; provide detailed device report, update software and configurations automatically to minimize system errors by measuring WAN response delay. System administrator can concentrate on problem-solving with the help of analysis tools and graphical device manager.
D15.2.13. System recovery procedures.
Considering all kinds of irresistible factors possible to occur, including equipments, servers, Internet access, and even earthquake, the system designed with redundancy will not fail due to any forseeable failure. Once the system is in trouble, the transactions will be switched to another site automatically though with performance loss.
System maintenance can be done by Network Management software, network analysis equipment to locate the troubled equipment. We will solve the problem or contact the equipment provider to help this.
Equipment Repair: We will make technical service contract with the equipment provider promising 4 hours to reach locale, getting rid of the fault or replacing another equipment. Start up the primary service and close the backup site. Log the maintain procedure.
Software Recovery: Start service on the standby server and synchronize database. Repair the system and import backup data, synchronize database and start service. Log the maintain procedure.
Internet Access: The registry-registrar must have IP address in different ISPs. So when one ISP is in trouble, it will not influence the domain registry service. Start the standby dedicated line to provide service, and collaborate with the ISP to solve the problem.
D15.2.14. Technical and other support.
Engineering Support: Eastcom agrees to provide Registrar with reasonable engineering telephone support (between 9 a.m. and 5 p.m. Peking time or at such other times as may be mutually agreed upon) to address engineering issues arising in connection with Registrar's use of the System.
Customer Service Support: During the Term of this Agreement, Eastcom will provide reasonable telephone and e-mail customer service support to Registrar, not SLD holders or prospective customers of Registrar, for non-technical issues solely related to the System and its operation.Eastcom will provide Registrar with a telephone number and e-mail address for such support during implementation of the RRP, APIs and Software. First-level telephone support will be available on a 7-day/24-hour basis. Eastcom will provide a web-based customer service capability in the future and such web-based support will become the primary method of customer service support to Registrar at such time. Whilst the default language of DRS is English, to date we will build registry systems in English, Chinese, French, Spanish, and Japanese.
¡¡
By signing this Registry Operator's Proposal, the undersigned certifies (a) that he or she has authority to do so on behalf of the registry operator and, on his or her own behalf and on behalf of the registry operator, (b) that all information contained in this proposal, and all documents attached to this proposal, is true and accurate to the best of his/her/its knowledge and information. The undersigned and the registry operator understand that any material misstatement or misrepresentation will reflect negatively on any application of which this proposal is a part and may cause cancellation of any delegation of a top-level domain based on such an application.
_______________________________
Signature
Yu Xudong______________________
Name (please print)
Vice President
Title
Eastern Communications Company Limited
Name of Registry Operator
_Sep 26,2000_________________________
Date
¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡ ¡¡(c) 2000 The Internet Corporation for Assigned Names and Numbers
All rights reserved.
Updated August 15, 2000